Please update your browser.
Download the latest version of a supported browser below to get the most out of this website:
Secure payments set to the Square standard
Businesses deserve protection from the moment a payment is taken. That’s why Square is invested in payments security from end to end.
Stay on guard and in the green with secure transactions
Our security services help seasoned development teams and small businesses manage bad actors and address customer concerns. The price? It’s included in the processing fee.

PCI compliance
To protect customers, credit card companies require merchants to follow a series of security guidelines to comply with the Payment Card Industry Data Security Standard, known as PCI compliance. As the merchant of record, we maintain PCI certification so you don’t have to individually validate your compliance.
No stress of maintaining and updating your compliance each year.
No expensive audits, assessments, or noncompliance fees.
No third parties needed to manage your compliance.
Expert dispute assistance
When card payments turn into disputes, we help businesses navigate the red tape. With the right documentation, we can advocate on your behalf with the bank and card network.
Allow our team of experts to help shepherd your dispute through the process.
Let us coordinate with the bank so you don’t have to spend hours going back and forth.
Keep track of active disputes and get instant dispute notifications in Dashboard.
Robust account protection
We have many layers of defense designed to keep hackers away from your money. Still, they can get ahold of your password or email address if those credentials have been compromised somewhere else online. Use our tools to enhance your security. We’ll monitor your login activity and block suspicious activity.
Set up 2-Step Verification to add a layer of security to your account.
Control who has access to your account through employee permissions.
Enable passkeys to securely log in with your device’s fingerprint scanner, facial recognition, or a PIN code.
Proactive fraud protection
Avoid losing dollars to fraudulent purchases. Square uses machine learning to look at payments from across our ecosystem and adjust our algorithms to account for new trends in fraud.
Our systems proactively monitor your payments to keep an eye on suspicious transactions.
Machine learning and human expertise work hand in hand to adapt our technology to the shifting fraud landscape.
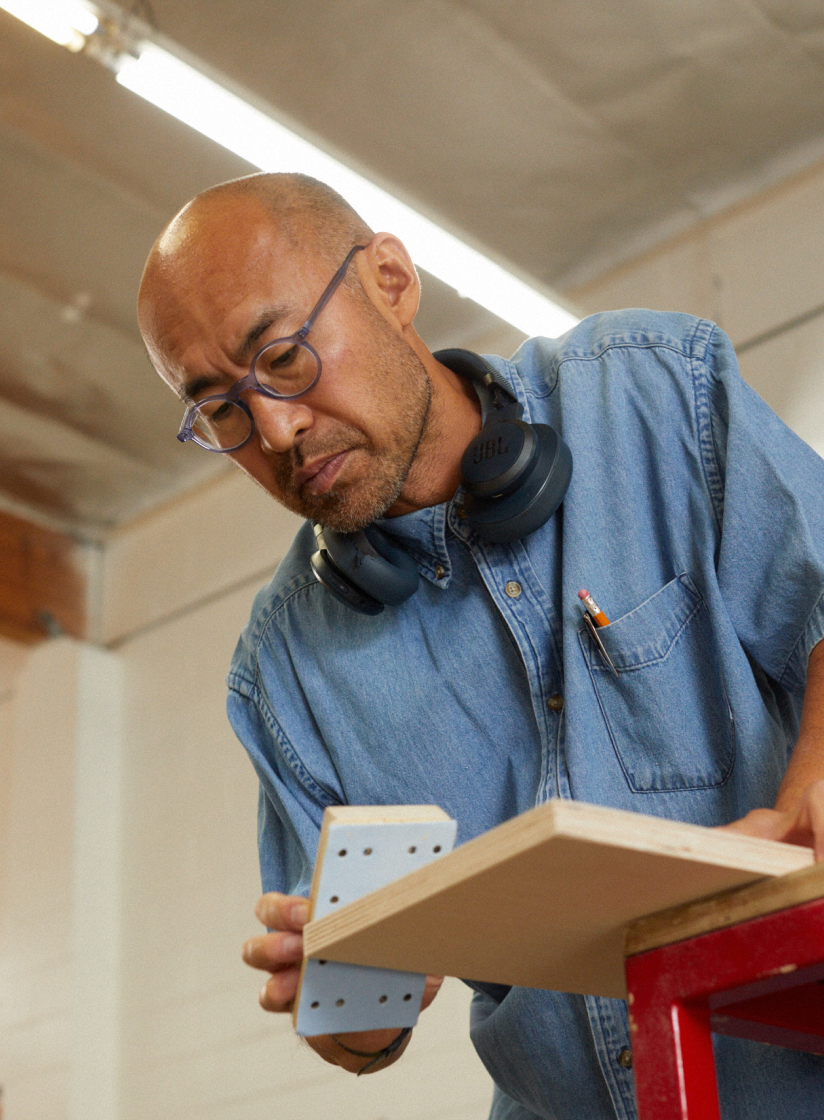
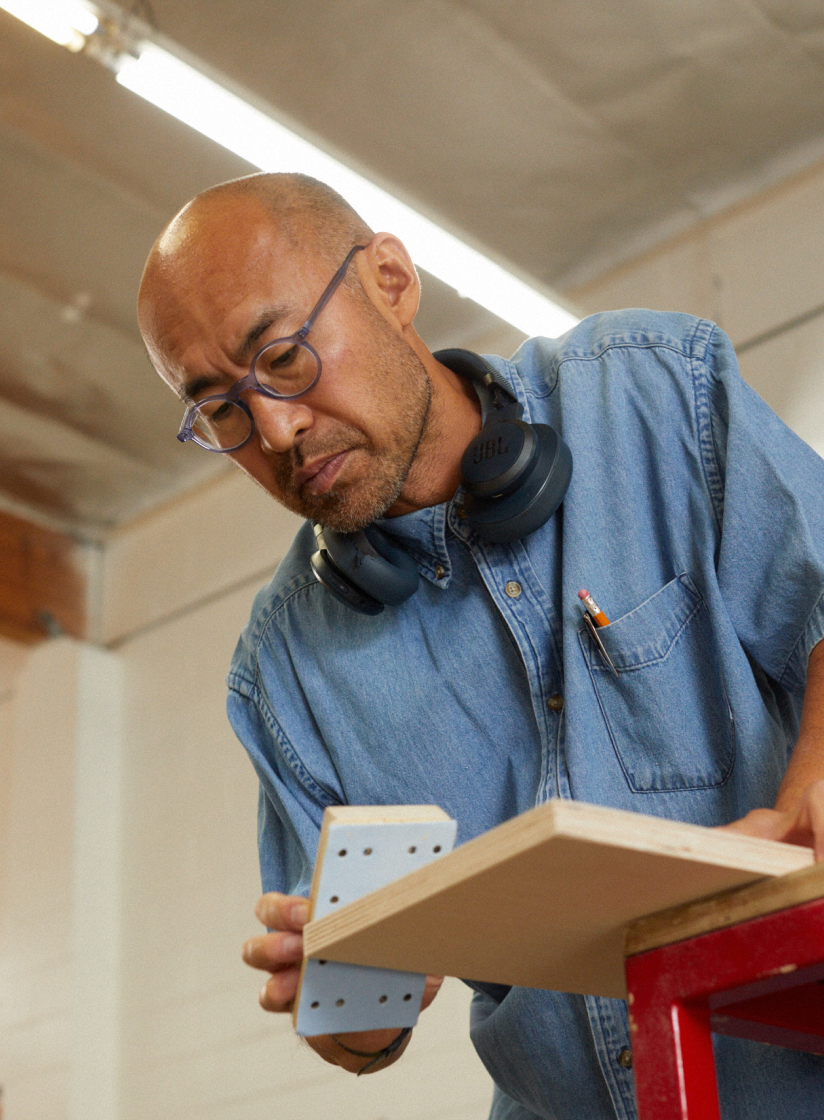
Businesses trust us. This is why.


Scale
Our team helps sellers avoid 177,000 disputes every year by sharing transactions with card networks and issuers directly to keep buyers informed of their purchases and to prevent disputes.

Expertise
Sitting on the Payment Card Industry’s Board of Advisors, we’ve helped evolve the PCI Data Security Standards for nearly a decade.

Credentials
ISO 27001 certified
PCI Data Security Standard, Level 1
Our security platform doesn’t sleep, so you can
Secure hardware and software
Every Square product is engineered for security from the ground up. It’s all designed and maintained by Square, so you don’t have to go through anybody else.
Payments hardware is secure out of the box with no lengthy setup.
In-house teams of engineers constantly monitor our server security.
Secure data
Our proprietary system ensures no unencrypted payment data touches your device or application. No card numbers. No magnetic-stripe data. No security codes.
All card-present payments are encrypted from end to end.
We use industry-standard cryptographic protocols and message formats to transfer data.
Secure organization
Secure card readers and in-depth defense on our servers are just the baseline. Yes, we stress-test our systems and keep ahead of malicious actors. We’re also committed to the highest standards of information security governance.
We’ve achieved the renowned ISO 27001 certification.
Square security is evaluated every day by public bounty researchers.
Spotted a vulnerability? Report it on Bugcrowd →
Tools and resources to support your security needs
Our customer support and online resources are here to investigate and resolve an issue so your business can keep moving.

Dedicated support team
Our Support team works side by side with our product, design, and engineering departments to maximize your customer experience. We’re ready to help you via phone, email, live chat, and social media.

Square Secure profile
Your encrypted, private profile stores documentation that helps us get a clear picture of the business you run and assess potential risks and unusual activity.

A library of resources
We have a large collection of education resources and a Seller Community where you can ask questions of other sellers.

Risk Manager
We’re always developing new ways to help you avoid card payment disputes and save money. Check out one of our latest: Risk Manager, which provides fraud insights and allows you to set custom alerts.
Prevent miscommunication and disputes in your industry














Professional Services
Create a custom contract for free.
Having a contract gives you legal leverage to collect payment if your customer misses progress payments or fails to pay for goods on time. Try one of our contract templates.¹
Food and Beverage
Create receipts easily.
Receipts can help provide proof of delivery for customers questioning their order. Generate a receipt for any successful payment, including quantities, discounts, and applicable taxes.
Retail
Manage risk and prevent loss online.
Risk Manager helps you detect fraud and prevent loss without slowing the growth of your online business. Create custom rules and automatically block suspicious cards. Get detailed explanations on each risky payment.
Unsure about your security? Let's change that.
Get business insights by signing up for marketing from Square.
Subscribe to our email list to receive advice from other business owners, support articles, tips from industry experts, and more.
Nice to meet you.
We think businesses are as unique as the people who run them. Get individualized content on the topics you care about most by telling us a little more about yourself.

Brush up on best practices.
Secure your business with Square.
Explore The Bottom Line and our Support Center to find educational resources about security and privacy.
¹ We’re glad to offer you tools to help improve your business. But it’s important to note that Square is not a law firm and this document does not constitute legal advice. Square provides this template to individuals who choose to prepare their own contractual documents for their private use. If you need legal advice as to the accuracy, sufficiency or enforceability of specific contract terms you should consult with a licensed attorney.